In today's digital age, sustaining solitude in on the web communication is tougher than ever. New reports show that more than 60% of web customers are worried about the protection of their messages and personal data. With the rise of cyber threats and data escapes, several people and corporations are looking at advanced tools for protected communication. One of the top alternatives emerging lately may be the secret note, allowing people to send sensitive and painful data with full confidence, ensuring communications are just available to the intended recipient.
What Is just a Secret Note ?
A secret note is just a electronic note or message that is encrypted and frequently self-destructs following being read. That ensures that painful and sensitive information is not saved on hosts for extended times, lowering the chance of unauthorized access. Several platforms now offer secret note characteristics included in secure message, and the engineering was created to be user-friendly without diminishing security.
Why Are Secret Notes Crucial Nowadays?
Privacy has changed into a cornerstone of electronic interaction. Data reveal that around 75% of people choose platforms that offer increased safety features like encrypted message or time-limited note access. Secret notes function a twin purpose—they protect particular interactions and help firms control confidential information without the chance of unintended exposure.
How Do Secret Records Work?
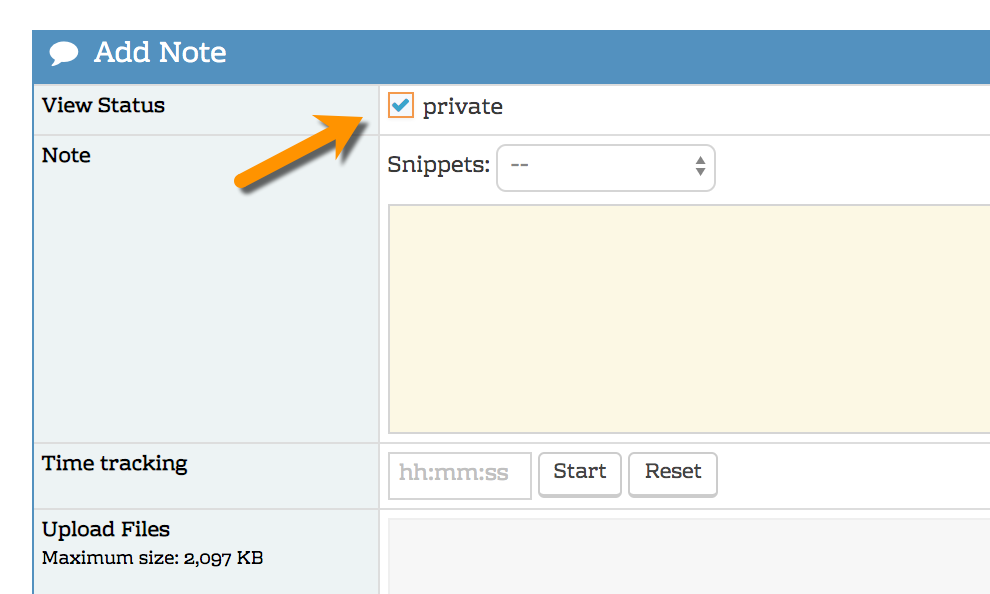
Secret records count on security calculations to ensure that the message content is just available to authorized users. Typically, a distinctive link or code is developed, that the receiver should use to gain access to the message. Many systems also include functions like auto-deletion, study statements, and limited access time, which offer extra levels of security.
Can Businesses Take advantage of Secret Records?
Absolutely. Businesses handling sensitive and painful client information, internal techniques, or financial information find secret notes specially valuable. According to a 2023 study, 68% of small-to-medium businesses noted an increased feeling of protection following employing encrypted communication tools. Using secret records for central memos or customer communication diminishes the chance of escapes and helps organizations conform to solitude regulations.
Are Secret Records Truly Private ?
While number program may guarantee absolute security, secret notes significantly lower coverage compared to standard email or messaging platforms. The combination of encryption, self-destruct timers, and restricted accessibility helps it be substantially tougher for third events to intercept or misuse the content. More over, the unknown or pseudonymous nature of some secret note methods gives another privacy coating, attractive to users who prioritize discretion.
Frequent Use Instances for Secret Records
Skilled Communication: Sharing sensitive and painful company information or economic documents.
Particular Messages: Giving confidential particular communications or reminders.
Cooperation: Groups can change sensitive and painful challenge changes securely.
Knowledge & Research: Teachers and researchers may reveal preliminary conclusions or unpublished work safely.
Critical Benefits of Applying Secret Notes
Enhanced Security: Protects information from undesired access.
Controlled Accessibility: Set time restricts and permissions for each note.
Easy Use: Many programs offer one-click formation and sharing.
Compliance Help: Assists businesses match information solitude regulations.
Potential Developments in Secret Records
Authorities estimate that the use of secret records can expand beyond personal and corporate messaging. Integration with AI tools for protected workflow automation and real-time security analytics probably will become standard. Additionally, mobile adoption is raising fast; new data indicates that around 50% of secret note exchanges now happen on cellular devices, showing the tendency toward on-the-go privacy.

Realization
With cyber threats on the increase and personal privacy becoming significantly useful, secret notes offer a trusted alternative for protected communication. By combining security, controlled access, and simplicity, these instruments inspire users to maintain confidentiality in equally particular and professional contexts. As technology evolves, the adoption of secret records is estimated to develop, making them an important part of modern electronic protection strategies.
